Ragini Ramalingam
The Oscar-nominated film, ‘The Imitation Game’ tells the story of Alan Turing, a cryptanalyst, who lived during the Second World War. The Germans created a device called the Enigma machine, which they used to send coded messages amongst themselves. The coded messages normally contained encrypted instructions for executing various war related missions. Though the Allied forces intercepted the messages they were unable to decrypt it. Even the simplest form of the Enigma machine had 15*10^18 possible combinations of keys for decryption, making it extremely difficult for the Allied forces to interpret the messages. However, Turing built a device which decrypted the messages and potentially shortened the war by two years.
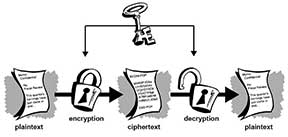
 So, what exactly is cryptography? Cryptography is the study of techniques for secure communication in the presence of unwanted parties, and has a rich history, steeped in math and science. Before the era of computers, cryptography was very simple. There was a method of encryption and those who were to receive an encrypted message would be informed of the method of decryption by the sender. But modern cryptography is based on algorithms and computer theory, making it much more complex, much harder to decrypt and hence secure.
So, what exactly is cryptography? Cryptography is the study of techniques for secure communication in the presence of unwanted parties, and has a rich history, steeped in math and science. Before the era of computers, cryptography was very simple. There was a method of encryption and those who were to receive an encrypted message would be informed of the method of decryption by the sender. But modern cryptography is based on algorithms and computer theory, making it much more complex, much harder to decrypt and hence secure.
Some of the earliest known ciphers were developed during Julius Caesar’s reign. The Caesar cipher is one of the simplest and well-known ciphers to mankind. For encrypting, we merely moved three letters forward from the intended letter and for decrypting we moved back three letters. For example, the word CAT would be encrypted as FDW. Variations on this cipher have also been used with the number of moves varying. For example, ROT-13 is the cipher in which we move13 steps forward or back, as the process of encryption and decryption is the same, only in reverse.
Then there are ciphers which code each letter to a specific number, symbol, or another letter, for which frequency analysis was used by cryptanalysts in order to decode messages. So, the polyalphabetic cipher was born. One of the first ones was called the Vignere Cipher, which uses some particular word as a key. Under the plaintext, we would write the keyword multiple times until there is a letter from the keyword under every letter of the plaintext. Every letter is assigned a number, A = 0, B = 1, and so on. So we add the numbers associated with the every letter in plaintext and the letter from the keyword below it, and take the modulus of that number with respect to 26. This gives us the letter in cipher text. Let us say we want to encrypt the word CAT. We decide to use the keyword “CIPHER”. The letters in the keyword “CIPHER” correspond to the numbers (2, 8, 15, 7, 4, 17). For example:
CAT
CIP
Now to code the letter “C” in the word “CAT”, we use the “C” (2) from “CAT and the “C”(2) from “CIPHER”, which gives us the number 4 (2+2), which codes to the letter “E”. Then, for “A”, we use “A”(0) and “I”(8) to get “I”. Finally, we will get the cipher text as: “CII”. Now can you try for the word “DOG” using the keyword “PLEASE”?
But so far, in all the cryptosystems discussed here, the sender and the receiver use the same secret key. This is not the safest method for transmission of information, so what could make it more secure? Adi Shamir (An Israeli cryptographer and co-inventor of the RSA algorithm along with Ron Rivest and Len Adleman) created the 3-Pass Protocol, which in retrospect is deceptively simple. It uses complicated modular arithmetic, but the principle is straightforward. Let’s say, Alice wants to send a message to Bob. The message is going to be passed in a suitcase. Alice locks the suitcase with her own lock, for which she is the only one who has the key. When Bob gets the suitcase, he cannot open it, but just attaches his own lock. Again, he is the only one who has the key. Now, he sends it back to Alice, who removes her lock and sends it back to Bob. Now Bob can unlock the box and read the message. So this is a way for Alice to communicate with Bob without exchanging or agreeing on a key. This is a form of public key cryptography, in which the key for encryption and the key for decryption are different, with the former being made public, and the latter private. RSA cryptosystem uses large prime numbers and concepts like Euler’s theorem to create its keys. However, the security of the RSA system hinges on the fact that factoring large numbers is difficult.
Computers have enabled us to develop more advanced ways of sending messages that other people cannot decipher. Cryptosystems have varying levels of security. Conditional security means that they are secure assuming certain conditions hold. For example, there is a cryptographic method called one time pad which makes use of a binary key, this binary key is only known to the sender and the receiver, and it is impossible to decode unless the interceptor also has the key.
 Can cryptography use techniques which aren’t steeped in algorithms and mathematical principles? As it turns out, it is possible. Quantum cryptography is a field of cryptological study in physics which uses quantum communication and quantum computation to break cryptosystems, or develop new cryptological methods. As quantum computers are still only a concept, quantum cryptography can only hypothetically break other systems, however it has been used to send and receive messages before. Quantum Key Distribution allows the transmission of a sequence of random bits across an optical network and also verifies if this sequence was intercepted or not.
Can cryptography use techniques which aren’t steeped in algorithms and mathematical principles? As it turns out, it is possible. Quantum cryptography is a field of cryptological study in physics which uses quantum communication and quantum computation to break cryptosystems, or develop new cryptological methods. As quantum computers are still only a concept, quantum cryptography can only hypothetically break other systems, however it has been used to send and receive messages before. Quantum Key Distribution allows the transmission of a sequence of random bits across an optical network and also verifies if this sequence was intercepted or not.
Cryptographic technology is used for much more than just sending messages during wartime. It is used by banks for online transactions. Time stamping, which is a technique that verifies that a certain document was sent at a particular time also uses cryptography. The creation of secure network communications and disk encryption are other uses. Cryptosystems keep getting tougher and stronger, as people find ways around them. That is why it will remain a growing and important field of science. Cryptography and Cryptanalysis continue to alter futures even today.
The author is a first year B Math (Hons) student at Indian Statistical Institute, Bangalore. She enjoys good music and coffee more than most things. She can be contacted at ragini.rama@gmail.com.
